Showing how HTTPS is more secure.
You have, at least once in your life come across the statement “Make sure xyz website uses HTTPS before entering your private information”
Well, spoiler alert, it’s true.
But what is HTTP?
The Hypertext Transfer Protocol (HTTP), is a system by which computers talk to each other across the internet(www).
It’s used by computers, smartphones and other devices (Client) to ask web servers to return the contents of a specific website. Communication between client computers and web servers is done by sending HTTP Requests and receiving HTTP Responses
What is HTTPS?
Hypertext Transfer Protocol Secure (HTTPS) is an extension of the Hypertext Transfer Protocol (HTTP). It is used for secure communication over a computer network, and is widely used over the Internet.
In HTTPS, the communication protocol is encrypted using Transport Layer Security (TLS) or, formerly, its predecessor, Secure Sockets Layer (SSL). The protocol is therefore also often referred to as HTTP over TLS, or HTTP over SSL. {- wikipedia}
In simple words, HTTP sends data across the web in plain text. Whereas HTTPS adds a layer of encryption to your data (SSL or TLS).
But how do hackers take advantage of this?
As we know HTTP does not encrypt your data while communicating with web servers, this means that a hacker (or anyone) can eavesdrop and look at your data.
Let us look how a hacker might go about doing this. To start off, we will be monitoring and looking at the activities of our system on HTTP websites as well as HTTPS websites and comparing them.
We will be using a Linux machine with the tcpdump tool installed. Alternatively you can also use Wireshark. But tcpdump is a CLI tool which gives us more options to refine our analysis.
tcpdump and Wireshark are packet analyzer tools which are used for network troubleshooting and analysis.
Getting started!
The first thing we will do is setup tcpdump to monitor all HTTP traffic. So fire up your terminal and enter the following command:
tcpdump -i wlan0 -A port http
Explanation
-i switch will only capture from the desired interface on your system. We have set it to wlan0. You can type “ifconfig” on your terminal and find your interface. You can also set it to any to capture traffic from all interfaces.
You can find specific port traffic by using the port option followed by the port number or protocol name. In our case we need to sniff HTTP traffic so we have mentioned the same.
-A will print each packet in ASCII. It helps us in capturing web pages.
After running the above command, let’s try to visit an HTTP website (http://testphp.vulnweb.com/) — This website is designed to be vulnerable so that it can be tested.
Now our terminal screen will look something like this:
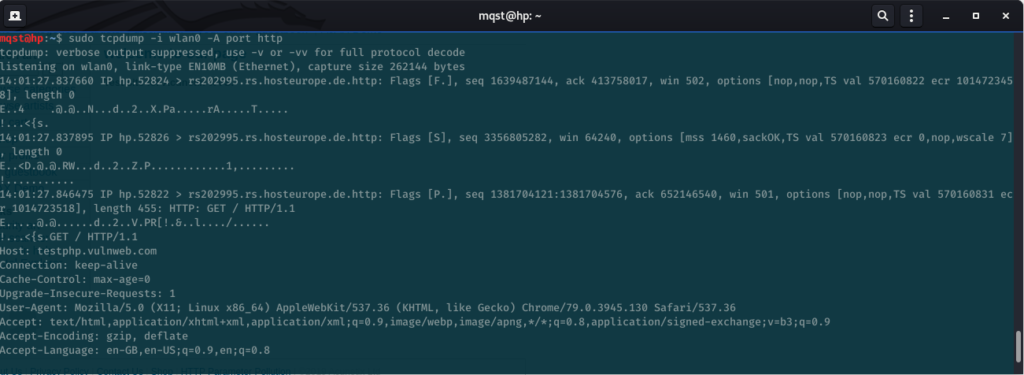
Now calm down, don’t freak out just yet. What you are seeing above is just your computer talking to the website (http://testphp.vulnweb.com/). Yup, that is exactly how computers talk to each other on the internet.
You will find all kinds of gibberish stuff on your terminal screen which will keep on increasing as you visit more and more HTTP websites.
Now if you look closely, you can see a collection of lines with words such as: GET, Host, Connection, etc.
Those series of lines are called the HTTP Request. It starts with GET or POST, etc and includes more stuff. As we keep going down, we will see different HTTP Headers. This HTTP Request is sent by our computer (Client) when we opened that website on our browser and is sent to the Server (website). Here you can see the name of the website too which we accessed on our browser.
But how would a hacker take advantage of this, you ask?
Well to start off, a person even looking at what websites you are accessing is scary enough. But what if there is a login page and you (Victim) try to login with your credentials?
Does that mean a hacker can look at your username and password too?
Again, spoiler alert, YES!!
Let’s look at how a hacker would do this.
Let’s visit the login page of the same website and try to enter any random credentials (http://testphp.vulnweb.com/login.php)
Let’s use the username as “test” and password as “password123”. Yes, i know, very secure.
Anyway, after we press login, we switch back to our terminal screen and scroll and find the HTTP Request with the login username and password.
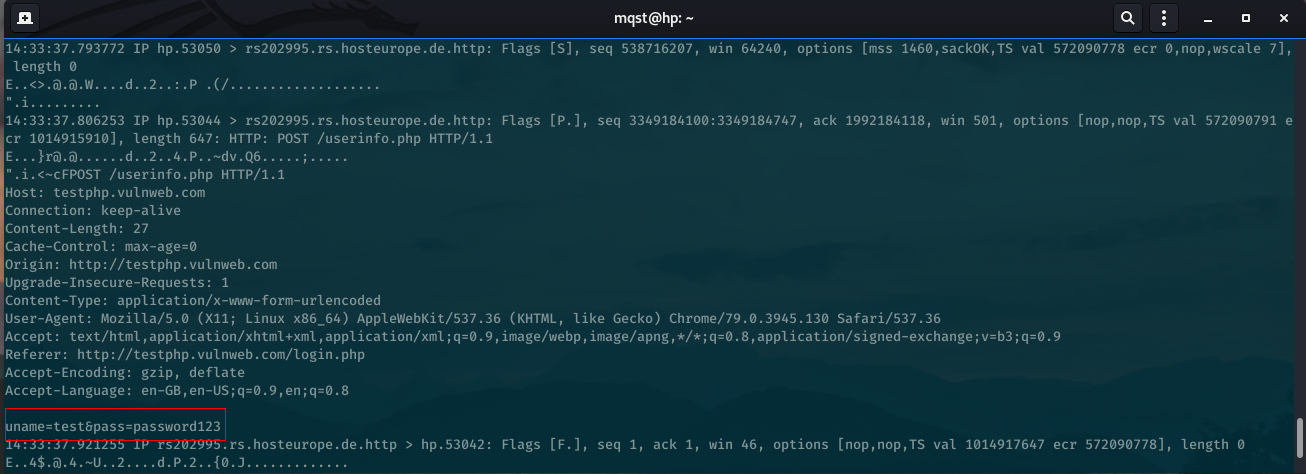
Bamm! After scrolling through all that http traffic, we find our HTTP Request with our victims username and password.
What if you don’t want to see all that http traffic and you only want to capture your username and password? Use the following command:
sudo tcpdump -i wlan0 -A port http | grep ‘uname’
grep helps us to find our “uname” parameter directly in all that http traffic and just gives us the line with the username and password.
Well done, you’re now a Hacker!
Will HTTPS also show the hacker my username and password?
Now let’s try all that again quickly but with HTTPS this time. Type the following command on your terminal:
tcpdump -i wlan0 -A port https
We have entered the same command but with HTTPS instead of HTTP. Let us open an https website and try to login. Let’s use rediffmail (https://mail.rediff.com/) and enter the same credentials as above.
This is what you will see on your terminal screen:

That’s right, NO username or password or any kind of HTTP traffic visible in plain-text. All you see is gibberish data being exchanged between you and rediffmail. This is because HTTPS encrypts point to point between applications. The gibberish data is actually encrypted data being sent to rediffmail. So as discussed in the beginning of this article, the http traffic will be encrypted by SSL or TLS.
The idea here is that HTTPS traffic that travels over the Internet is confidential, a random router or person who happens to capture your packages cannot decrypt the HTTPS without the decryption key.
Conclusion
Now we have practically seen why it is not a good idea to enter your private information on a website using HTTP and why HTTPS is way more secure.
We also saw an attack called “Man-in-the-Middle” — (MiTM) attack. And how a hacker would passively monitor all your traffic.
But wait..if you are as keen as me, you would ask yourself a question:
All the stuff shown above was performed on the same computer and the traffic was also monitored from the same computer. How does that make me a “Hacker” ?
or
How would a hacker perform the same “MiTM” attack on other victims on the network?
To get those answers, you’ve gotta read the next article – [https://www.muqsitbaig.com/blog/how-you-could-get-hacked-at-a-coffee-shop/ ]
Make sure to share this article if you liked it and leave a response if you have any queries.
If you want more such scripts to collect usernames and passwords through Tcpdump (HTTP) be sure to check my:
Github — https://github.com/mqst
Linkedin —https://www.linkedin.com/in/muqsit-baig
Hackerone — https://hackerone.com/mqst
Thanks for reading! Subscribe to the mailing list for more updates.


